Видео с ютуба Zero Trust Compliance

Citrix How To: Zero Trust access based on antivirus compliance

Что такое сетевой доступ с нулевым доверием (ZTNA)? Модель, структура и технологии Zero Trust.

Zero Trust Club Episode 4 - The Compliance Playbook: Meeting Security Standards with Zero Trust

How Zero Trust Architecture Enhances Regulatory Compliance

IGA in 2026: Zero Trust, Compliance & Omada’s Leadership Explained by QKS Group

Enforce Governance and meet Compliance for a zero-trust, least-privilege security posture

Zero Trust Workshop - MAM Compliance and Conditional Access

Zero Trust Explained in 4 mins
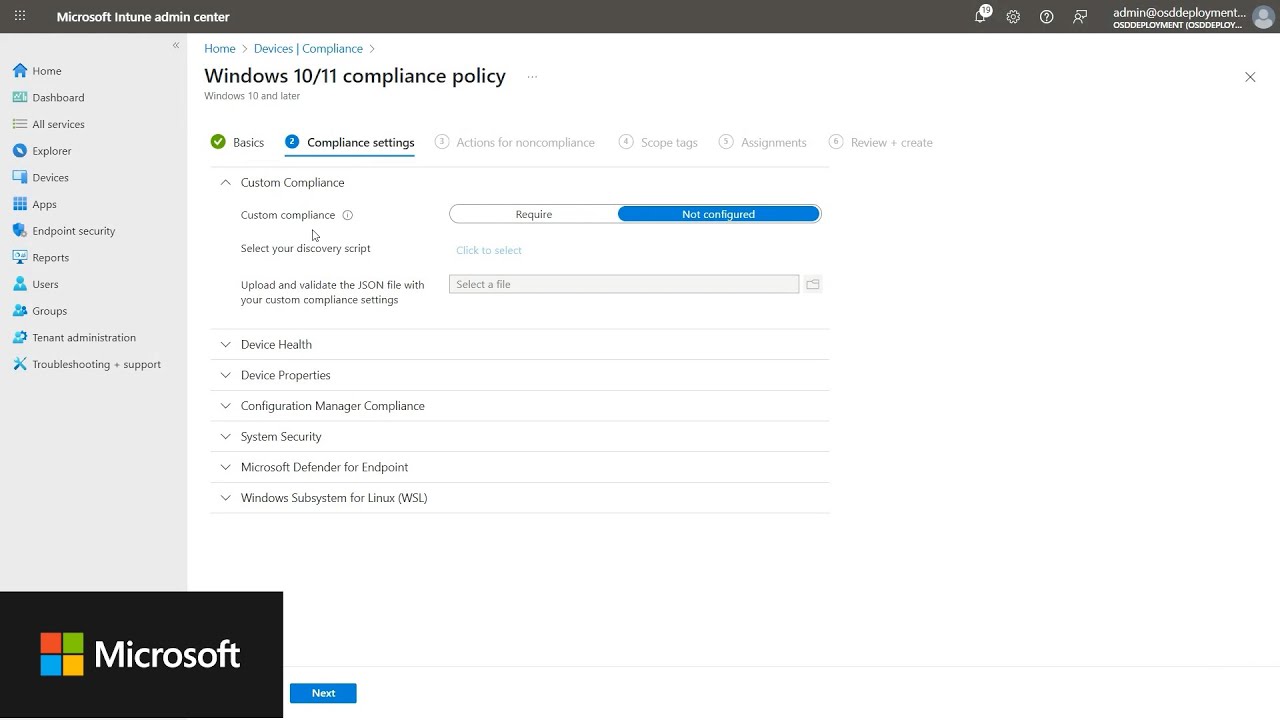
Zero Trust Workshop - Compliance Policies in Intune

Simplify Compliance with Zero Trust
Zero Trust in Action: Tackling Compliance & Securing File Data Exchanges Using MFT

How to Create a Comprehensive Zero Trust Strategy for Enhanced Security | SANS Webinar

CAASM and the Role of Zero Trust

Citrix How To: Zero trust access based on Workspace App version compliance

Zero Trust + Open Source: A Practical Compliance Blueprint | Rakia Finley, Copper & Vine Studio

Zero Trust Unleashed: Fortifying Data and Navigating Compliance in the AI Era

LF Live Webinar: Solving for Compliance and Zero Trust with Istio Ambient Mesh

Zero Trust Compliance Panel Discussion

Simplifying Zero-Trust Network Access and Accelerating Zero-Trust Compliance

Citrix How To: Zero Trust access based on geolocation compliance